caplon decoding & network recording
High-Performance Network Data Capture from Germany
We are the data capture experts.
Against the background of increasingly complex infrastructures and rising data rates, guaranteed loss-free data capture is becoming more and more important and is the prerequisite for reliable and meaningful data analysis.
Faulty measurements with packet losses can lead to the fact that coherent sessions cannot be evaluated meaningfully and thus to incomplete and faulty analyses.
We capture every bit. For reliable evaluations and meaningful analyses.

High performance data acquisition for 5G and broadband services
- highly scalable architecture that can grow with increasing data rates
- lossless data acquisition at > 100 Gbit/s without packet loss using dedicated FPGA-based data acquisition boards
- high accuracy due to nanosecond time stamps
- completely passive and feedback-free operation (data acquisition via mirror ports of a switch or via a TAP)
- the right configuration for every application from 1 Gbit/s to more than 100 Gbit/s network to disk performance
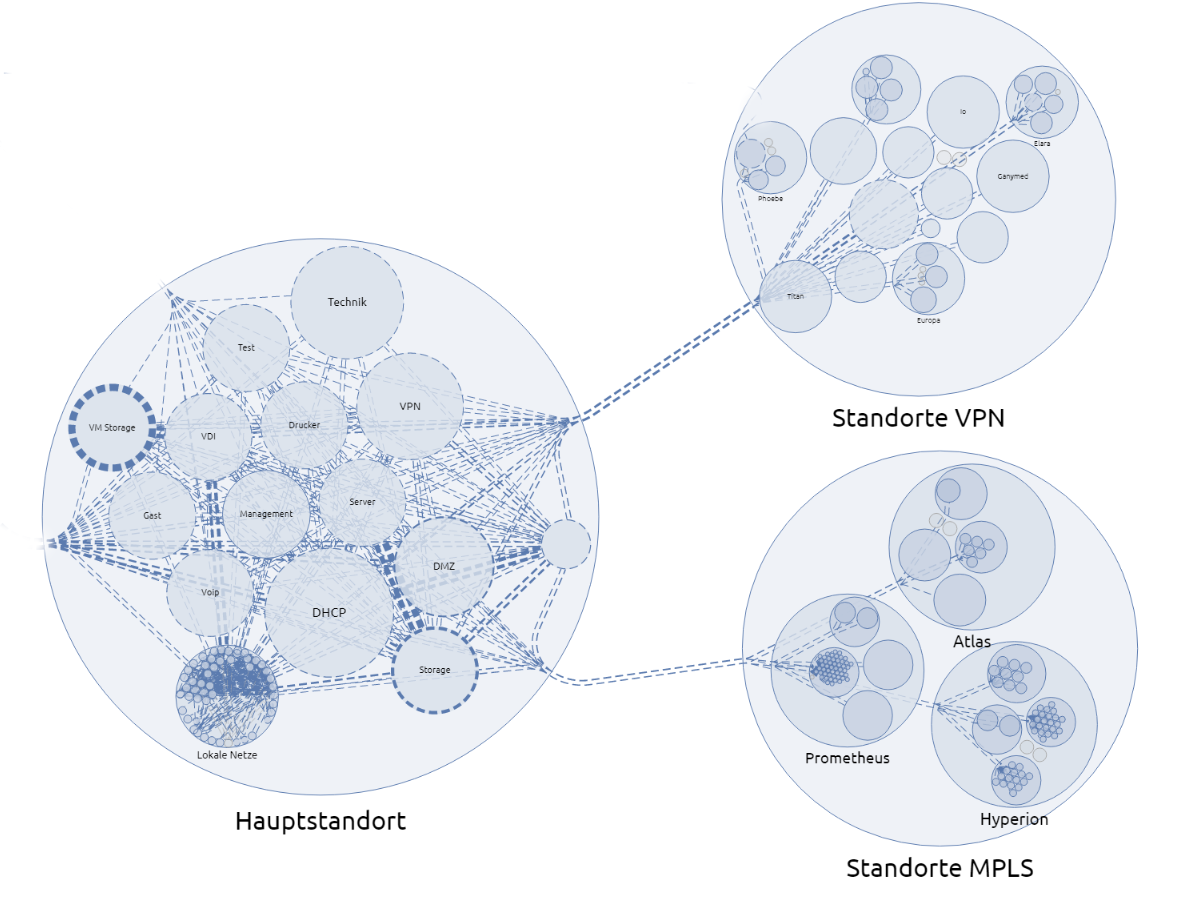
Tracing in distributed and hybrid structures
- monitoring of spatially widely distributed and multi-site structures
- individually powerful data acquisition systems:
Edge boxes in the OT area, caplon© network probes, caplon© appliances with umbrella function, ... - With caplon© virtual appliances and caplon© virtual probes, traffic within and between virtualization hosts can also be recorded.
- The system architecture allows individual adaptations to customer requirements and optimization of costs.
- Flexible connection types with 1/10/40/100 Gbit/s trace ports (copper and fiber optic)
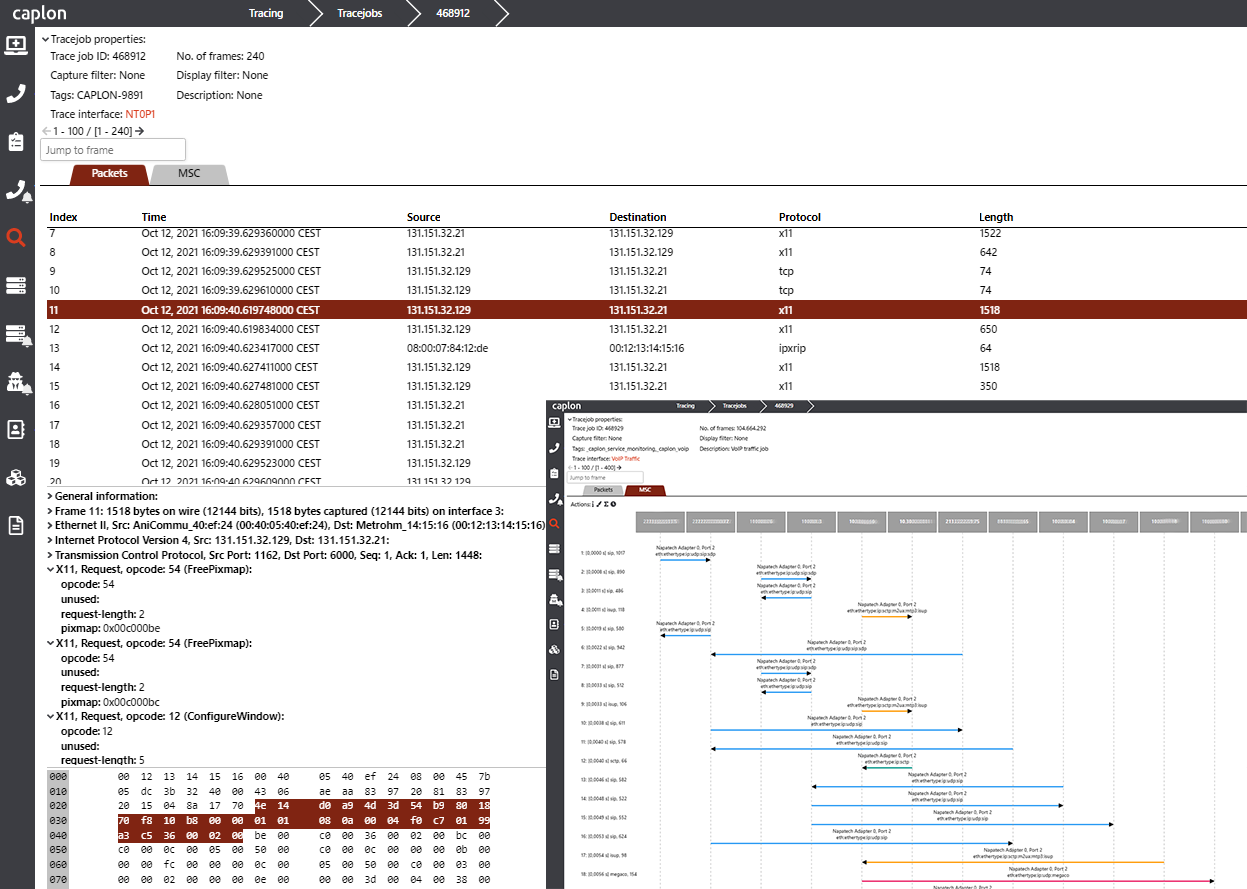
Save time during troubleshooting
- Find errors in the communication of your IT and OT systems
- Reduce integration efforts when commissioning new systems
- Verification of measurements and tests in the network
- Decoding of all common IP-based protocols in the ITC area and the areas of ICS and SCADA
- Decoding of proprietary protocols (on request)
- Detection and optional removal of packet duplicates
- Annotation of network packets with the information where they were captured in the network
- Display of network packets directly in the browser or in Wireshark with custom Wireshark plugin
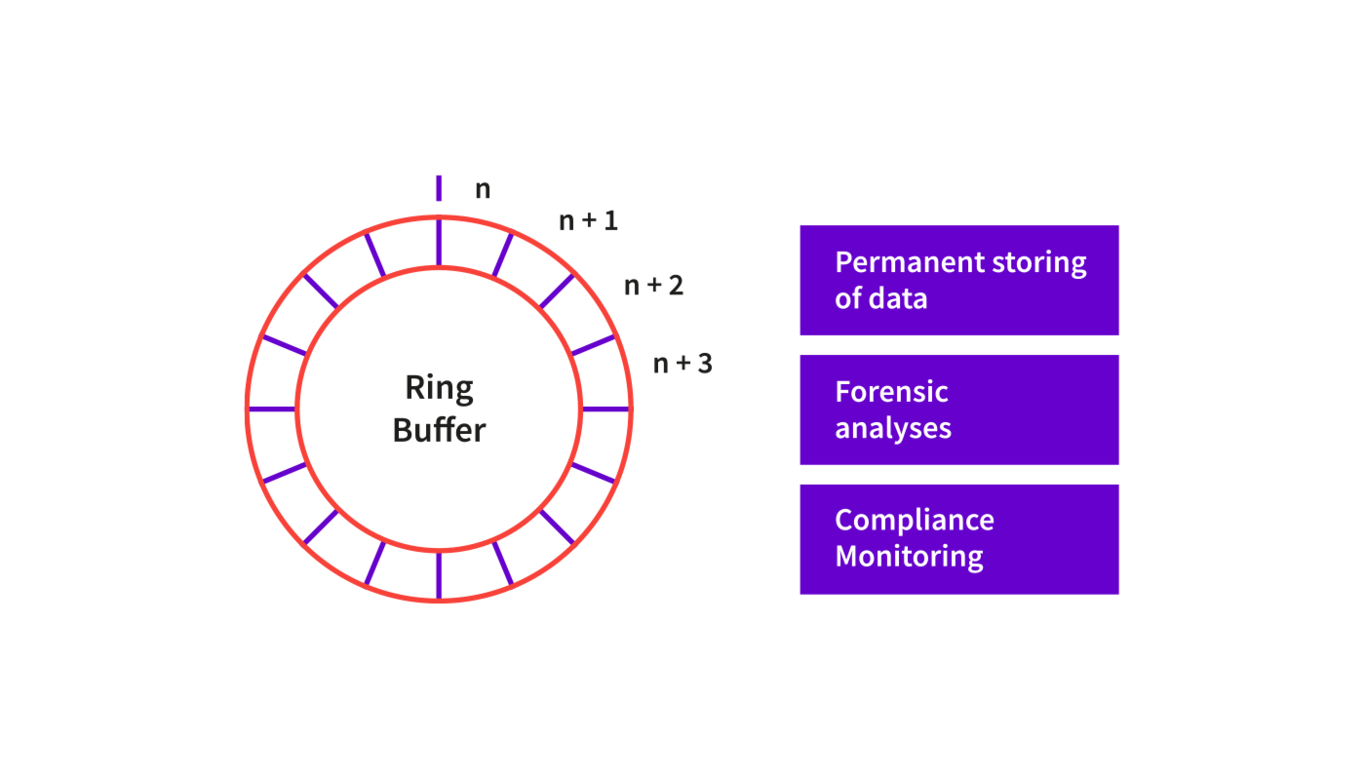
Permanent circumstantial evidence - traveling into the past
- Permanent circumstantial security through continuous network recording ("flight recorder for the network")
- Solving sporadically occurring problems
- Securing digital traces for forensic analyses of security incidents
- Compliance monitoring - making adherence to compliance requirements verifiable
- Backing up data by creating ring buffer snapshots
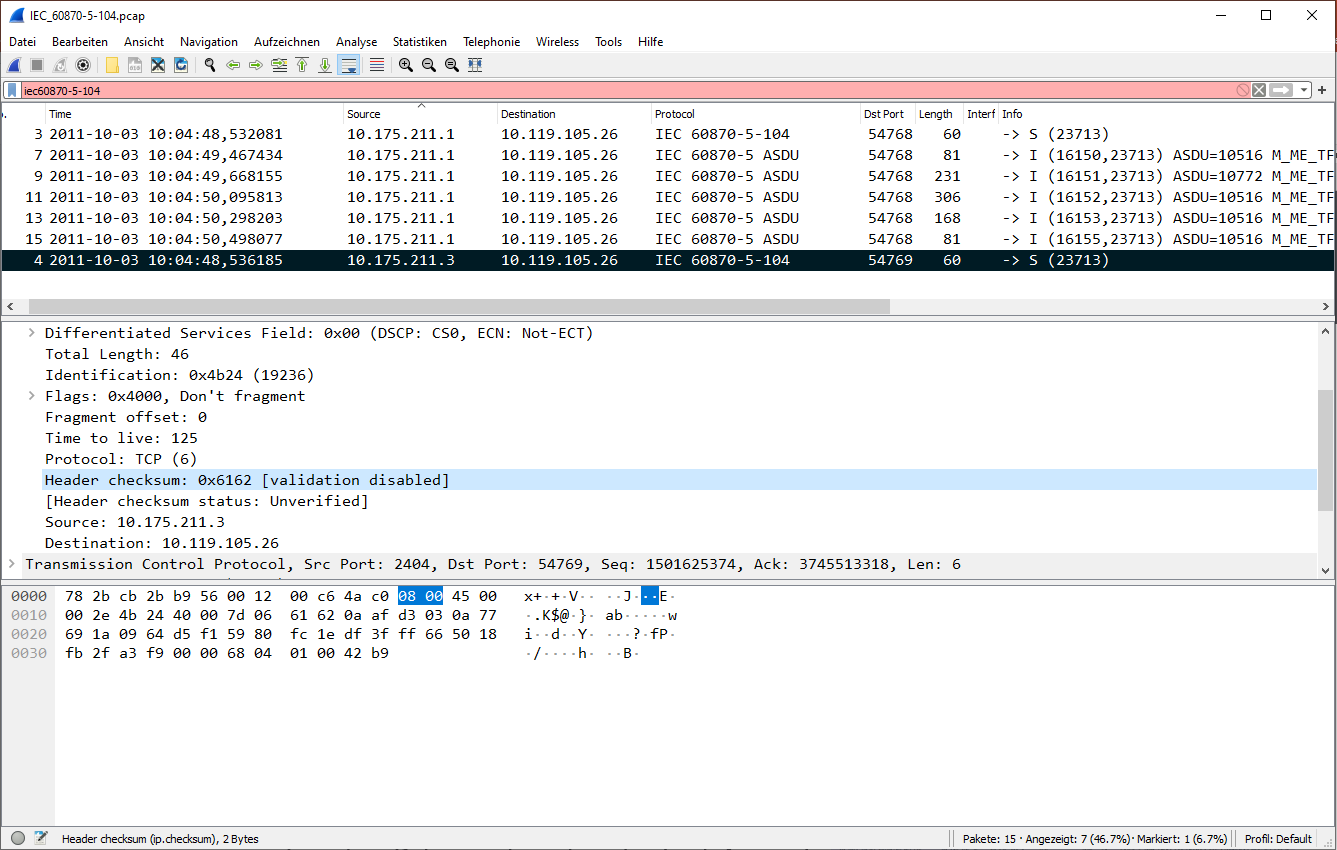
Wireshark integration
- Extensive integration of Wireshark via Wireshark plug-in module (for Linux, Windows and MAC OS)
- Live tracing in distributed structures: analyze pre-filtered traffic from different network segments online in one trace file
- Tracing with Wireshark with considerably reduced risk of data misuse by applying appropriate authorization profiles
- Tracing with Wireshark without access to personal data or critical infrastructure data through online pseudonymized network data with caplon© privacy protection
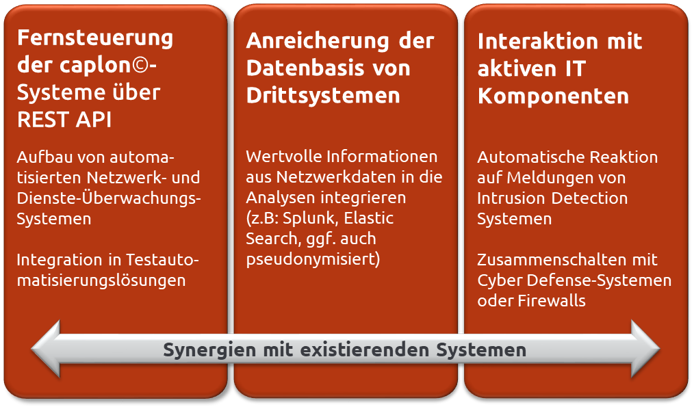
Synergies with existing systems through open interfaces and automation capability
- Integration into automated monitoring systems and coupling with intrusion detection systems
- Integration into test automation solutions
- Provision of valuable information from network data for third-party systems, e.g. SIEM systems
- Interaction with active IT components (cyber defense systems, security data collection, firewalls, ...)
advantages caplon Network Decoding & Recording
Easy to integrate
- Fast and easy rollout
- completely passive - no negative interactions
- smart entry due to scalable and modular design
- synergies with existing systems through open interfaces
Safe investment due to smart licensing model
- CAPEX and OPEX model
- Stand alone licence - linked to dongle, not tied to server hardware
- Lifetime licence - no need to purchase new hardware when it is end-of-life
Guaranteed lossless data acquisition
- Complete data acquisition even in high-speed networks
- No measurement errors due to unrecorded packets
Example scenario IDS appliance:
3% packet loss = approx. 10% missing alerts = potentially undetected intrusion attempts.
Risk minimisation for data misuse
- Fine-grained access to network data: Network segments, layers and depth of analysis per user or role, ...
- Protection of personal and critical infrastructure data through pseudonymisation of network data (caplon© privacy protection)
